Bear in mind the film Groundhog Day? Bull Murray performs a fairly self-centered weatherman who finds himself in a time loop on Groundhog Day.
Home windows directors might have comparable emotions to Murray’s with regard to vulnerability CVE-2021-43890. First patched in December 2021, Microsoft introduced in December 2023 that it has detected assaults within the wild and patched the problem once more.
If that sounds complicated, it’s. What Microsoft failed to say is that the primary patch has by some means been undone since April 2023.
Appx installer spoofing vulnerability in Home windows
The vulnerability report refers back to the difficulty as a spoofing vulnerability in Appx installer in Microsoft Home windows. Microsoft developed the ms-appinstaller Uniform Useful resource Identifier to help the downloading and set up of apps immediately from Web servers.
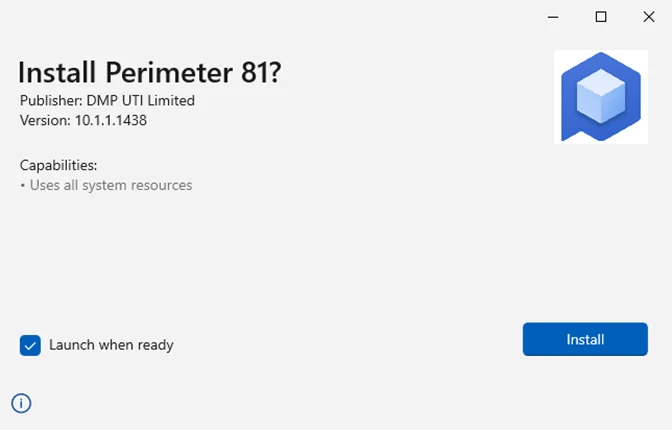
In different phrases: customers who clicked on ms-appinstaller hyperlinks would get an set up immediate equally to the one displayed on the screenshot above.
Whereas it nonetheless required the consumer to hit the “set up” button, the dearth of a distinguished “cancel” button led to undesirable installations. A click on on the x-icon on the prime of the window cancelled the method.
Activation of set up would obtain and set up the malware on the gadget.
Microsoft describes the method within the following method: “Customers who click on the hyperlinks to the installers are offered with the desktop App Installer expertise. If the consumer clicks “Set up” within the desktop App Installer, the malicious utility is put in and finally runs extra processes and scripts that result in malware set up.”
Microsoft’s weblog publish on its Safety weblog reveals that it noticed a number of assaults that make use of App Installer to contaminate Home windows gadgets. The performance is disabled by default in accordance to this Microsoft help web page. Directors might allow it, nonetheless. What Microsoft fails to say within the publish is that it disabled the performance in December 2021 already as a response to abuse of the performance.
Will Dormann was among the many first to identify this lacking piece of data in Microsoft’s announcement.
What Microsoft additionally doesn’t reveal in its announcement is when it disabled the performance by default. Günter Born thinks that the December 2023 safety updates are the almost certainly choice, however Microsoft by no means revealed this. Born discovered a single reference on the internet by a Microsoft Solutions consumer who acquired the “can not open app package deal” error message when attempting to put in an app utilizing the ms-appinstaller protocol.
The outline informs the consumer that the protocol has been disabled.
System directors might need to learn by Microsoft’s complete publish on the Safety weblog. It consists of details about three malwares that used the vulnerability in addition to an extended listing of suggestions.
Other than ensuring that App Installer construct 1.21.3421.0 is used, Microsoft recommends the next mitigations:
- Deploy phishing resistant authentication strategies.
- Implement conditional entry authentication power.
- Educate Microsoft Groups customers and apply finest safety practices for Microsoft Groups.
- Educate customers to evaluation sign-in exercise and mark assaults.
- Make customers use Microsoft Edge or one other browser that helps Microsoft’s Defender SmartScreen know-how.
- Educate customers about clicking on hyperlinks and verifying hyperlink targets.
- Educate customers that they double-check software program that’s put in, e.g., to ensure the writer is authentic.
- Configure Microsoft Defender for Workplace 365 to recheck hyperlinks on click on.
- Allow a number of safety features.
Greater than half of Microsoft’s ideas are about educating customers.
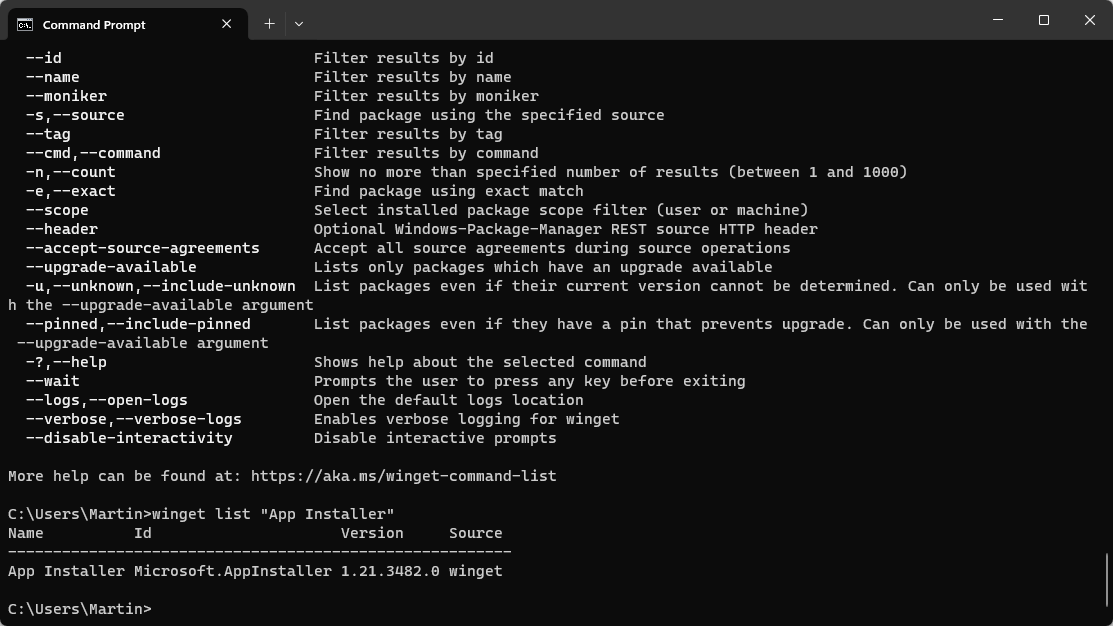
You possibly can test the AppInstaller model within the following method:
- Open a command immediate window, e.g., by opening Begin, typing cmd and deciding on Command Immediate from the choices.
- Kind winget listing “App Installer” and press the Enter-key.
Verify the model that’s returned. You possibly can improve the appliance utilizing the command winget improve Microsoft.AppInstaller.
Now You: have you ever used App Installer previously to put in apps?
Thanks for studying..




