Many industrial computer systems are susceptible to a set of vulnerabilities that exploit flaws within the processing of startup logos throughout boot.
Safety researchers at Binarly have disclosed safety vulnerabilities in system firmware utilized by pc producers through the boot course of. The vulnerability impacts x86 and ARM-based units.
The set of vulnerabilities is present in BIOS software program created by completely different corporations, together with the three largest unbiased bios distributors AMI, Insyde and Phoenix. These are extensively used within the business, as an example in computer systems by Intel, Acer or Lenovo. Alex Matrosov, CEO at Binarly, says that about 95% of all computer systems use firmware from the three bios distributors.
Binarly says that it estimates that nearly any gadget produced by these distributors is susceptible “in a method or one other”.
In easy phrases, LogoFail exploits vulnerabilities in picture parsers that affected units use to show vendor logos throughout boot. Completely different picture parsers are used to show completely different picture sorts, and “they’re rife with vulnerabilities” in keeping with Matrosov.
A hacker wants to exchange the seller picture with a specifically ready one to use the vulnerability and execute arbitrary code on the machine. Binarly explains that attackers could retailer malicious emblem pictures on the EFI System Partition or inside unsigned sections of a firmware replace. The photographs are then parsed throughout boot and this initiates the assault on the gadget.
The assault permits attackers to bypass safety features comparable to Safe Boot. Binarly notes that this additionally impacts hardware-based Verified Boot methods, together with Intel Boot Guard, AMD {Hardware}-Validated Boot and ARM TrustZone-based Safe Boot.
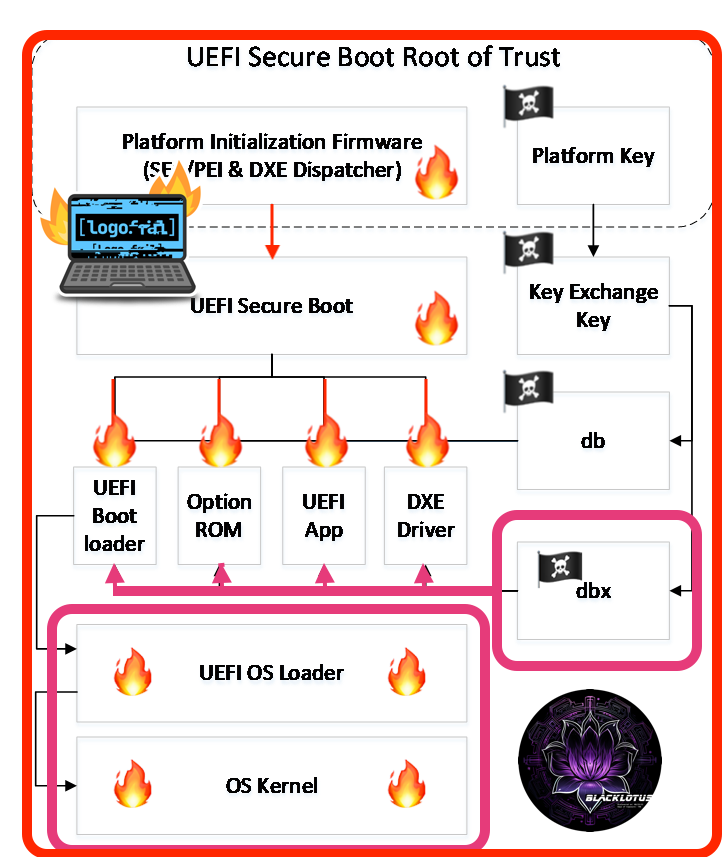
Binarly believes that the attacker might be able to bypass “most endpoint safety options” and combine a persistent stealth firmware bootkit on the system. In different phrases, attackers could exploit LogoFail to compromise the safety of many pc methods.
Assaults and safety
Attackers want to achieve administrative entry on course units to use the vulnerability. This may be achieved by malicious payloads planted on the system, as an example by getting the person to run malicious software program, or by exploits.
As soon as entry is gained, the attacker would exchange the distributors boot emblem with a malicious emblem, which the gadget would then load throughout boot.
An attacker would be capable to disable UEFI safety features, comparable to SecureBoot, modify the boot order and execute malicious software program to contaminate working methods.
Firmware updates can be found or shall be launched for a number of the affected units. Directors could need to test for firmware updates for units that they handle that tackle the vulnerabilities. Not all units will obtain firmware updates, nevertheless. Particularly units which can be not in help could not obtain them.
A seek for “gadget title firmware replace” or “gadget title drivers” ought to return the motive force obtain web site of the producer of the gadget.
Customers on units with out firmware updates have to be further cautious and use protections to keep away from the preliminary assault on the gadget (which wants administrative entry).
Extra details about the vulnerability is discovered on the Binarly web site and on the CERT database.
Thanks for studying..




