About six years in the past, vulnerabilities had been found that affected most Intel and AMD processors. The vulnerabilities, Spectre and Meltdown, may be exploited to learn delicate information from attacked pc programs.
Intel launched an replace for one of many Spectre variants, disclosed formally on March 8, 2022. Microsoft carried out mitigations in consumer and server variations of Home windows as a response to this.
These are disabled by default. The primary cause for this appears to be potential efficiency impacts that comes with the implementation.
This information walks you thru the steps of configuring Home windows to allow the mitigations and discovering out in case your processor is affected.
Is your processor affected?
The very very first thing you could wish to do is verify in case your processor is on Intel’s checklist of affected CPUs.
- Whether it is on the checklist, you could allow the mitigation to guard the system in opposition to potential assaults.
- If it isn’t on the checklist, you’ll be able to skip the rest of the article.
Right here is how you discover out:
- Open Begin > Settings > System > About and verify the listed processor.
- Load the next two useful resource web sites: Nist.gov and Intel’s Affected Processors web site.
Examine to see if the put in processor is listed on these web sites. You might wish to use the browser’s search to seek out the data shortly.
Microsoft’s Registry tweak to guard in opposition to the vulnerability
In case your processor is on the checklist, you could change the Registry keys to allow the mitigations.
Notice: implementation might have an effect on efficiency. Whereas I can’t advocate not enabling these mitigations, the chance of assaults in opposition to dwelling PCs is more often than not neglectable.
Backup: it’s extremely really useful to again up the system drive earlier than implementing the mitigation. Not with Home windows’ Backup App, which is ineffective for the aim, however with a full backup program like Paragon Backup & Restoration Free.
Here’s what you want to do on Home windows units and shoppers to mitigate CVE-2022-0001:
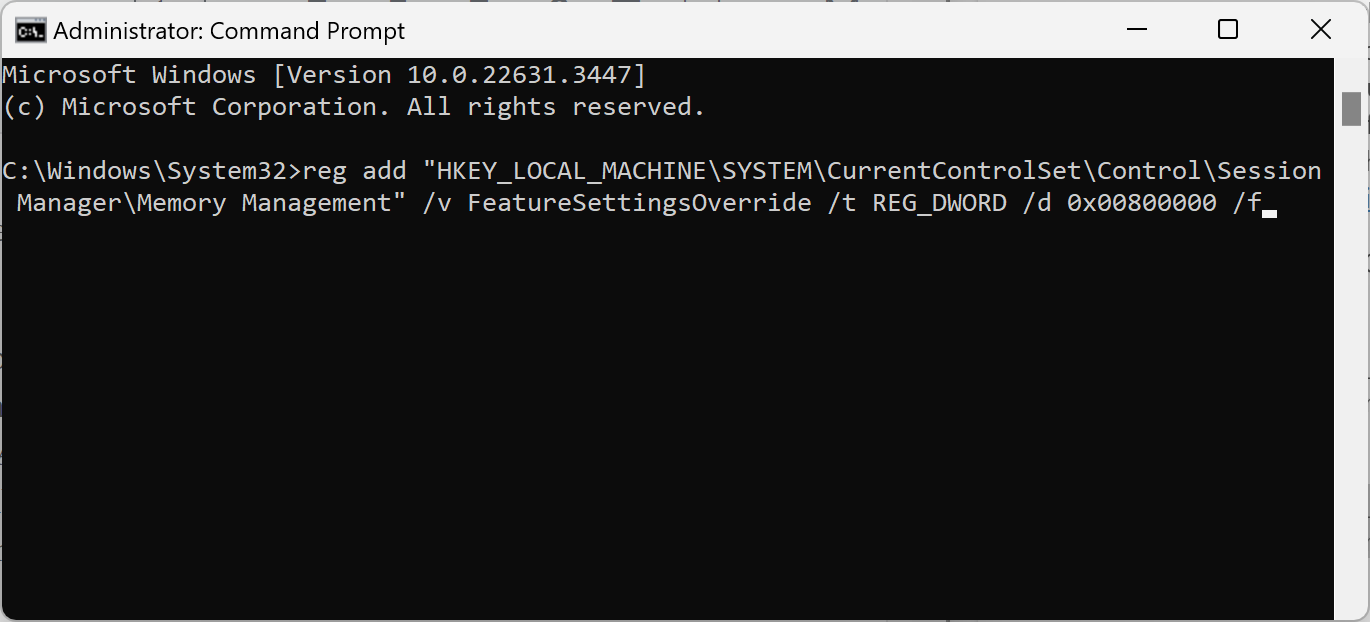
- Open Begin, kind CMD, and choose Run as administrator. This launches an elevated command immediate window.
- Affirm the UAC immediate by deciding on sure.
- Execute the next two instructions by pasting them and urgent the Enter-key after every:
- reg add “HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSession ManagerMemory Administration” /v FeatureSettingsOverride /t REG_DWORD /d 0x00800000 /f
- reg add “HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSession ManagerMemory Administration” /v FeatureSettingsOverrideMask /t REG_DWORD /d 0x00000003 /f
- Restart the pc after each Registry keys have been added.
Tip: you could wish to monitor efficiency to be sure that day-to-day operations are usually not severely impacted by the mitigation.
Curiously sufficient, Microsoft has additionally revealed how Linux customers might mitigate the vulnerability: “Specify spectre_bhi=on on the kernel command line”.
Closing Phrases
Whereas it could be crucial for organizations to implement the mitigation, dangers of assaults are comparatively low for dwelling customers.
What about you? Have you ever carried out Spectre / Meltdown mitigations in your PCs? (by way of Neowin)
Thanks for studying..




